TechSpot is celebrating its 25th anniversary. TechSpot means tech analysis and advice you can trust.
Why it matters: The Google Play Store is notorious for harboring apps that contain malware, adware, or some flavor of spyware or fleeceware. A little-known fact is that hackers are increasingly turning to pre-installed apps to do their misdeeds, but researchers are once again trying to raise attention to this growing trend. Millions of affordable Android phones come with a large number of pre-installed apps, and hackers only need to subvert one. Solving this problem, however, is a much more difficult task compared to dealing with rogue apps that make it into the Play Store.
Last month, we learned that malware had been discovered in 60 Android apps with over 100 million downloads – another black eye for the mobile operating system that has an estimated three billion active users worldwide. Malicious developers regularly exploit various loopholes in Google’s app vetting process to create apps that steal login credentials or fleeceware that squeeze as much as $400 million per year from users by tricking them into signing up for expensive in-app subscriptions.
However, researchers at Trend Micro are sounding the alarm about the growing trend of Android devices that come with malicious software pre-installed. While you can easily remove an app you’ve downloaded from the Play Store, dealing with malware baked into system apps or device firmware is a much more difficult task.

Android’s open nature allows manufacturers to create a wide range of phone models and target price-conscious consumers with more affordable options, but it also opens the door for hackers to sneak in malicious code before those devices even leave the factory floor. And this risk also applies to other Android devices – everything from smartwatches to tablets, set-top boxes, and smart TVs.
Senior Trend Micro researcher Fyodor Yarochkin says pre-installed malware has become a lot more common in recent years partly because of a race to the bottom among mobile firmware developers. Once it became unprofitable to sell firmware, many of them started offering it for free.
As you’d expect, there’s a catch to this new business model – many of the firmware images analyzed by Trend Micro contained bits of code described as “silent plugins.” The researchers have discovered over 80 flavors so far, but only a few have seen widespread distribution. The more popular ones are being sold underground and marketed on Facebook, YouTube, and various blogs.
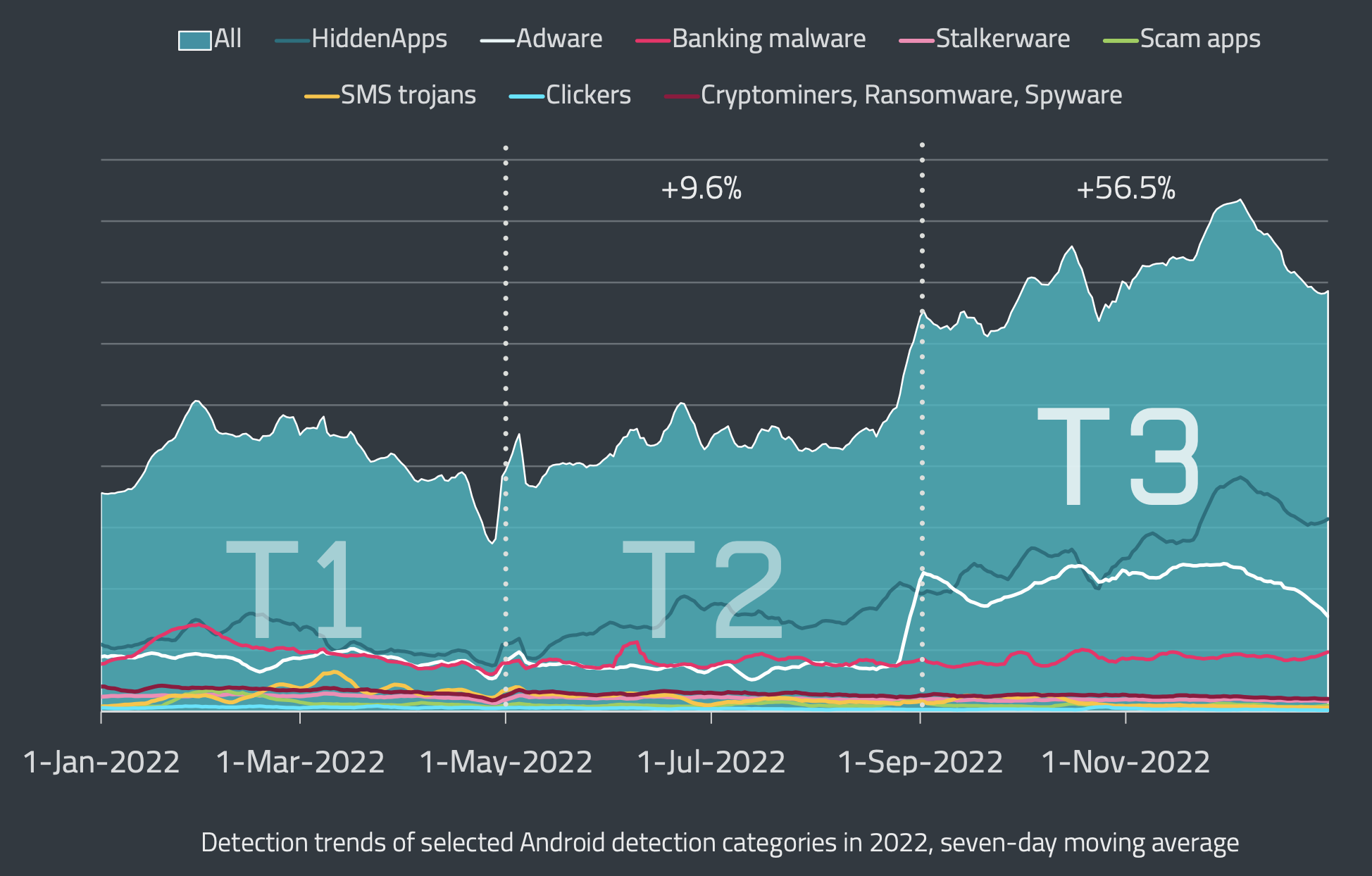
Data: ESET Threat Intelligence
Some of these plugins allow cyber criminals to “rent out” Android devices for up to five minutes at a time and use them to steal login credentials or other sensitive user information. Others are capable of downloading additional malware onto the infected device.
Researchers estimate that millions of infected devices are in use around the world, with a large portion concentrated in Eastern Europe and Southeast Asia. Interestingly, the criminals themselves claim that 8.9 million Android devices are loaded up with their silent plugins.
Trend Micro was able to confirm the malware was present in phones from at least 10 vendors, most of them Chinese. The firm suspects an additional 40 vendors are affected, but researchers are more interested in finding out where along the supply chain the infection is more likely to occur.
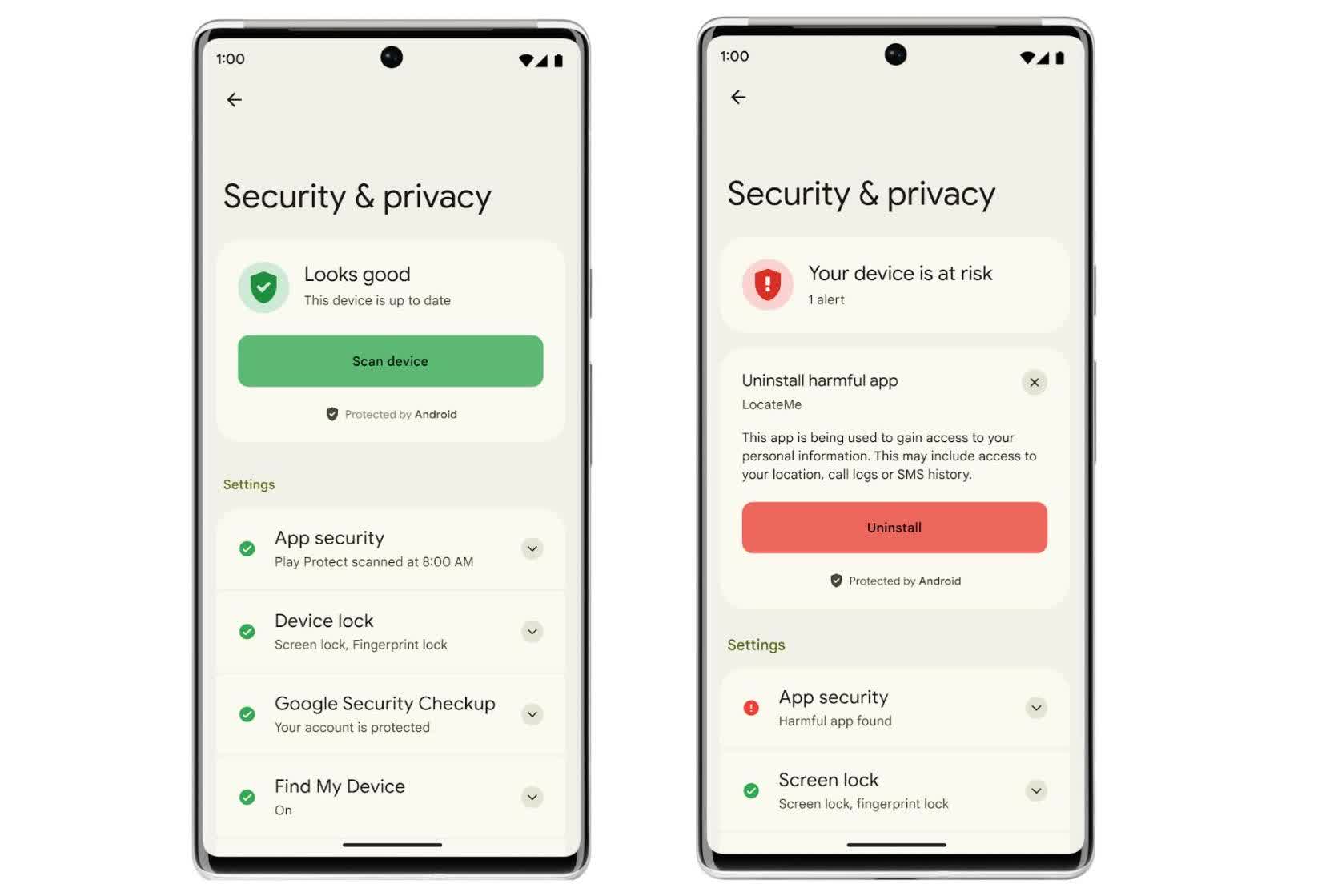
Play Protect can usually spot rogue apps from the Play Store, but what about silent plugins?
Google has known about pre-installed Android malware for years, but can’t easily solve the problem due to how little control it has over the complex OEM Android supply chain. Cheaper phones tend to use the Android Open Source Platform (AOSP) and come with anywhere between 100 and 400 pre-installed apps – all it takes is infecting one of them.
It also doesn’t help that as many as 225 device manufacturers regularly leave diagnostic software on Android phones, which essentially enables backdoor remote access for spyware and censorship tools. This behavior has been observed in a lot of Chinese brands as well as big names like Oppo, OnePlus, Realme, and Xiaomi. Some like Chinese-owned Gigaset, which sells phones in the EU, were found to have buried a malware auto-installer in a system update app.
Back in 2019, Google Project Zero researcher Maddie Stone revealed the existence of an SMS and ad fraud botnet called Chamois that had affected at least 21 million Android devices in previous years through pre-installed malware. The company found that vendors would often unknowingly incorporate Chamois code into their Android distributions because they were easily fooled into believing it was a legitimate ad service.
Also read: Does Android need saving? If yes, here’s how to do it.
Since then, Google has put a lot of effort into perfecting Google Play Protect and expanded its capabilities to monitor pre-installed apps on Android devices for malicious behavior. That said, hackers keep finding ways to bypass these protections, and they’re even developing lucrative business models around it on the dark web. A recent Kaspersky analysis found that accessing these malicious services costs anywhere between $2,000 and $20,000.
As for what you can do to protect yourself, Yarochkin recommends you go higher-end and stick to brands like Samsung and Google which supposedly have better supply chain security. Most mobile antivirus apps are ineffective against real security threats, so don’t bother with them unless you want to end up like thousands of users who downloaded password-stealing malware disguised as antivirus tools.
Image credit: Luis Andrés Villalón